Developers
Discover the latest industry trends, get ahead with cutting‑edge insights, and be in the know about the newest Gcore innovations.

Your cloud provider goes down. Applications fail. Customers can't access your services. And because you've built everything around a single vendor, there's nothing you can do but wait. For organizations locked into one cloud platform, this

Imagine discovering that migrating your company's data to a new cloud provider will cost hundreds of thousands of dollars in egress fees alone, before you've even touched the re-engineering work. Or worse, picture being in Synapse Financial

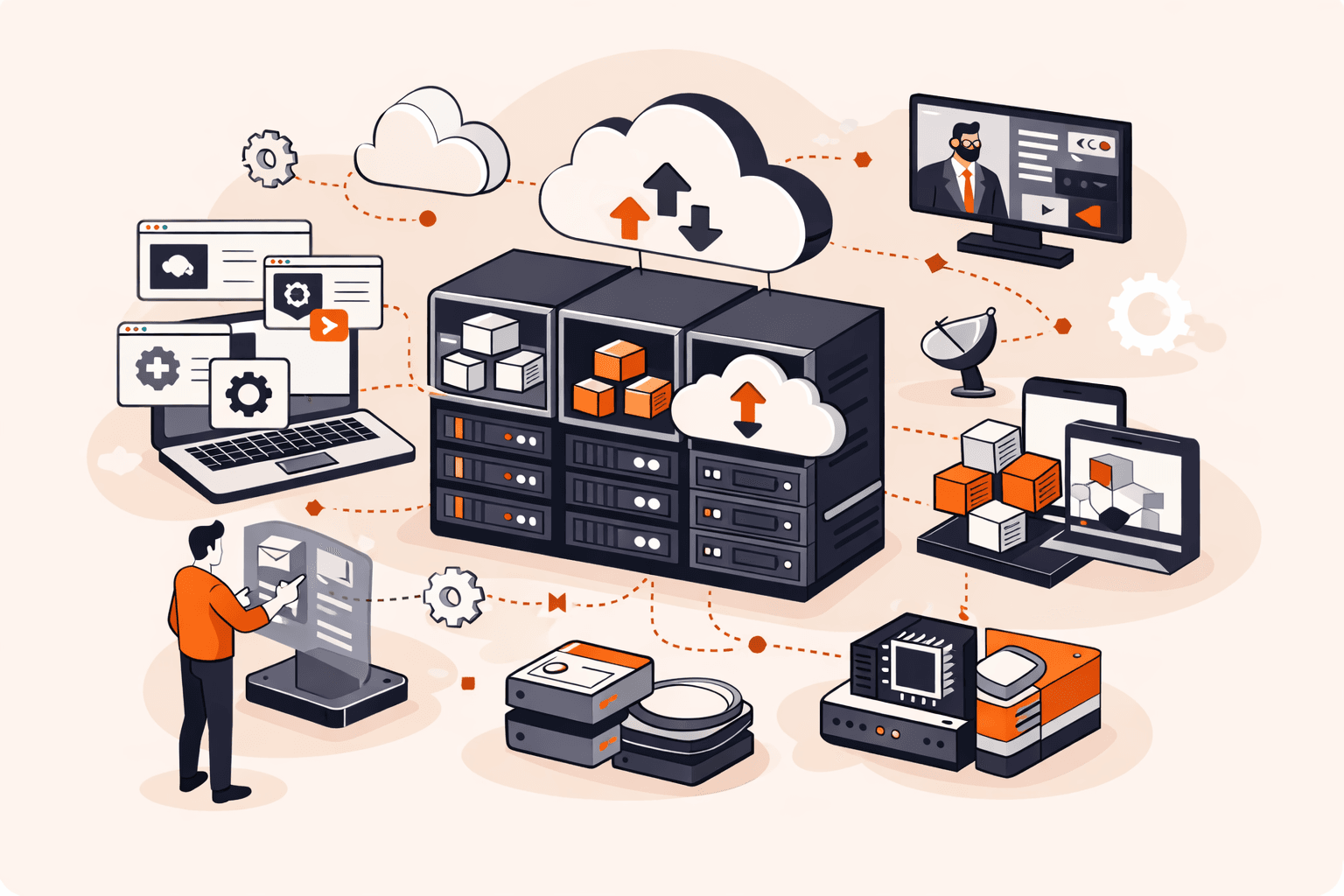
You're watching a video on your phone during your commute when it suddenly buffers, pixelates, and freezes, despite having full bars. Meanwhile, your friend streams the same content flawlessly on their laptop at home. Behind the scenes, str

Picture this: a foreign government issues a legal order forcing your cloud provider to hand over sensitive patient records, classified research data, or critical national infrastructure details. You can't stop it. This isn't hypothetical. G

Your database gets compromised. Customer records disappear. Credit card data ends up for sale on the dark web. SQL injection attacks remain one of the most prevalent web application vulnerabilities in 2024, consistently appearing in top ten
Your login page just got hammered with 10,000 password attempts in under a minute. Your API servers are buckling under a flood of requests. Legitimate users can't access the service while infrastructure costs spike. Without proper controls,
Your physical servers are sitting idle at 15% to 20% CPU utilization while you're paying for 100% of the power, cooling, and hardware costs. Meanwhile, your competitors have consolidated 10 to 15 applications per server, pushing utilization
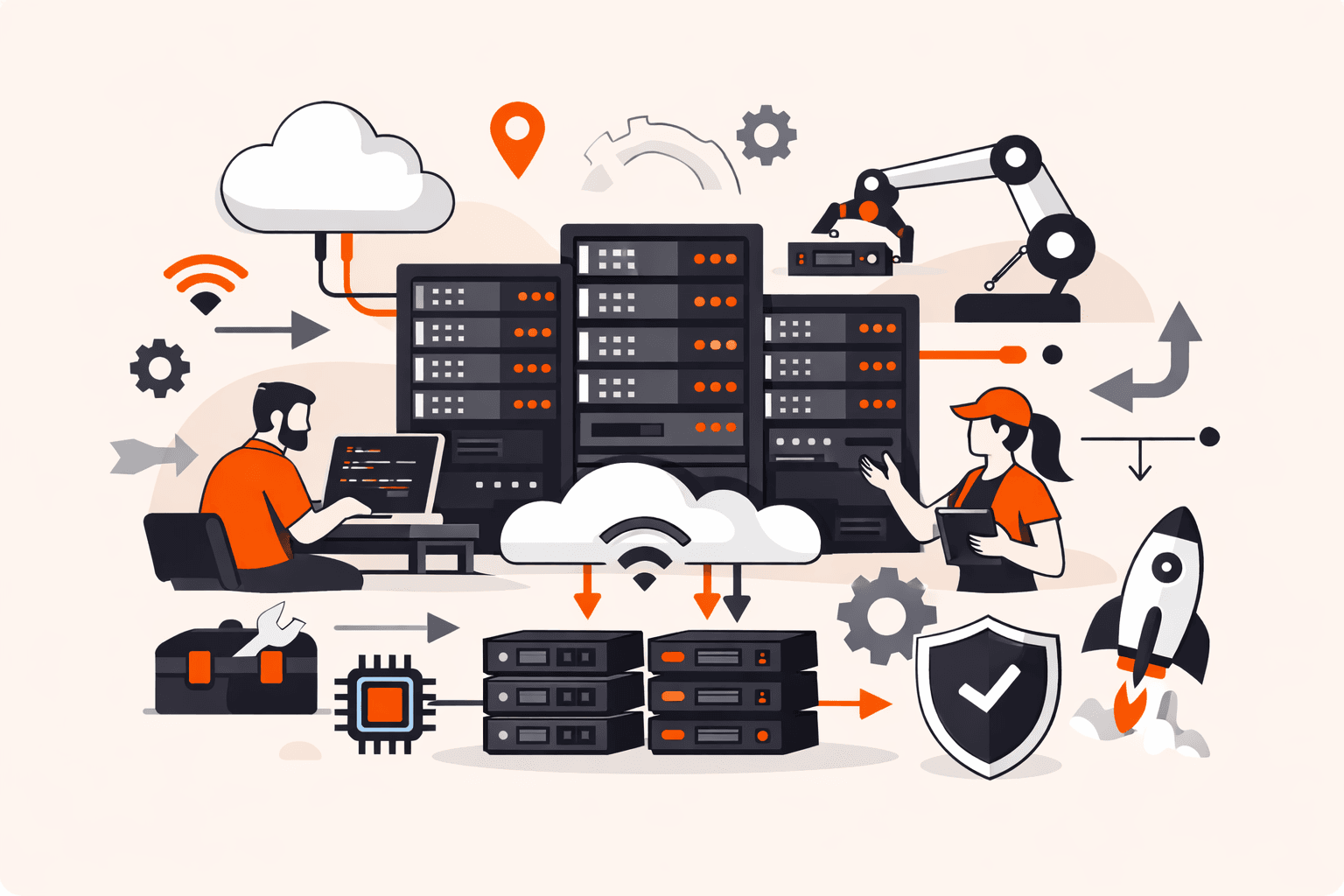
Your IT team just got approval for 50 new servers to handle a product launch. Manual setup means weeks of work, and here's the kicker: OS installation alone eats up to 90% of total provisioning time. Meanwhile, your competitors are deployin

You click a link in what looks like a routine email from your bank, and within seconds, $5,000 vanishes from your account, transferred to a stranger while you were simply logged in to your banking app. Many legacy web applications have vuln

You've logged into your banking app, checked your balance, and closed the browser. But here's what you don't see: an attacker is now inside your account, moving money and accessing sensitive data, without ever needing your password. Session
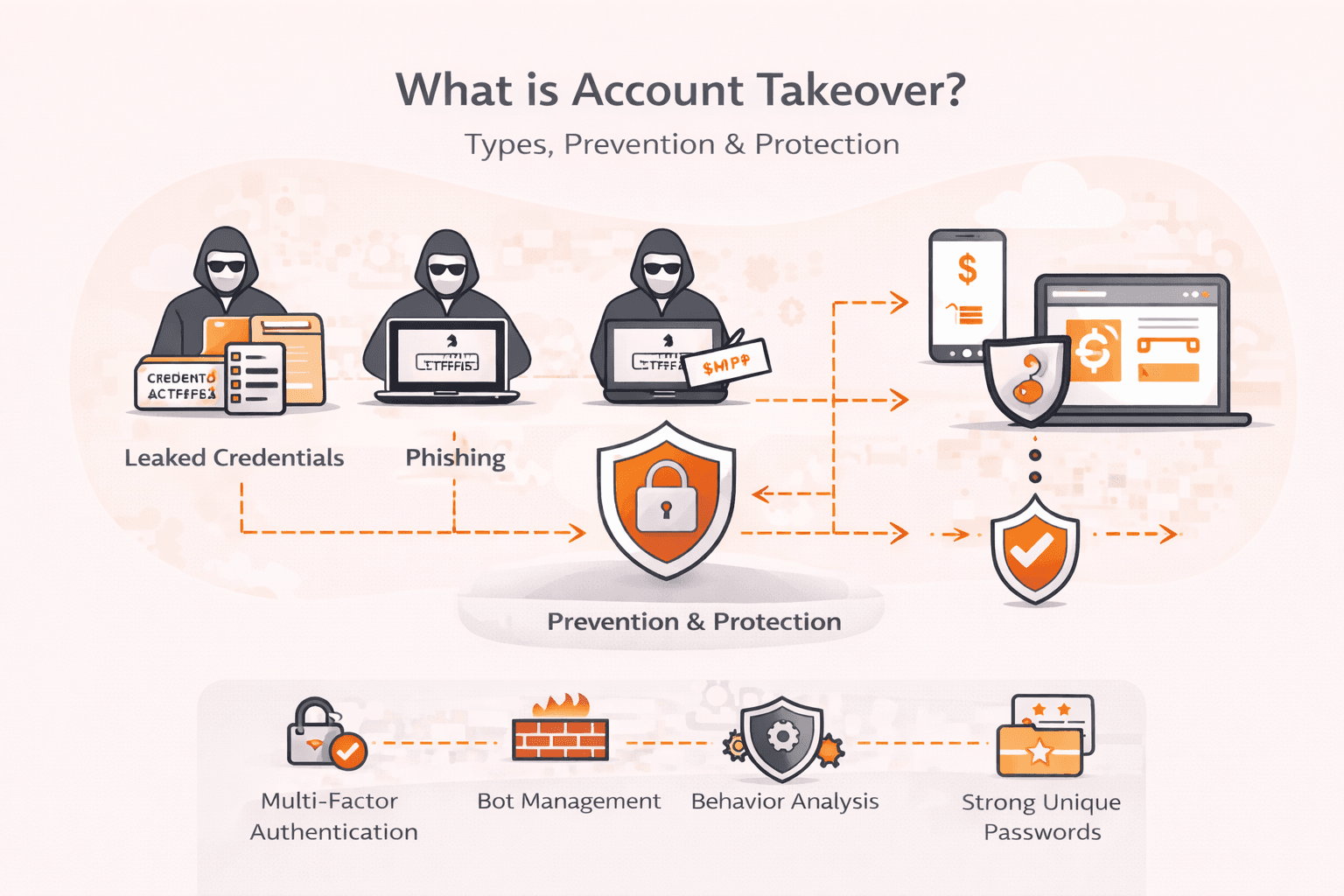
Your CFO's email account gets compromised overnight. By morning, cybercriminals have downloaded client banking information, stolen sensitive financial data, and grabbed credentials to your company's bank accounts. This isn't hypothetical, i
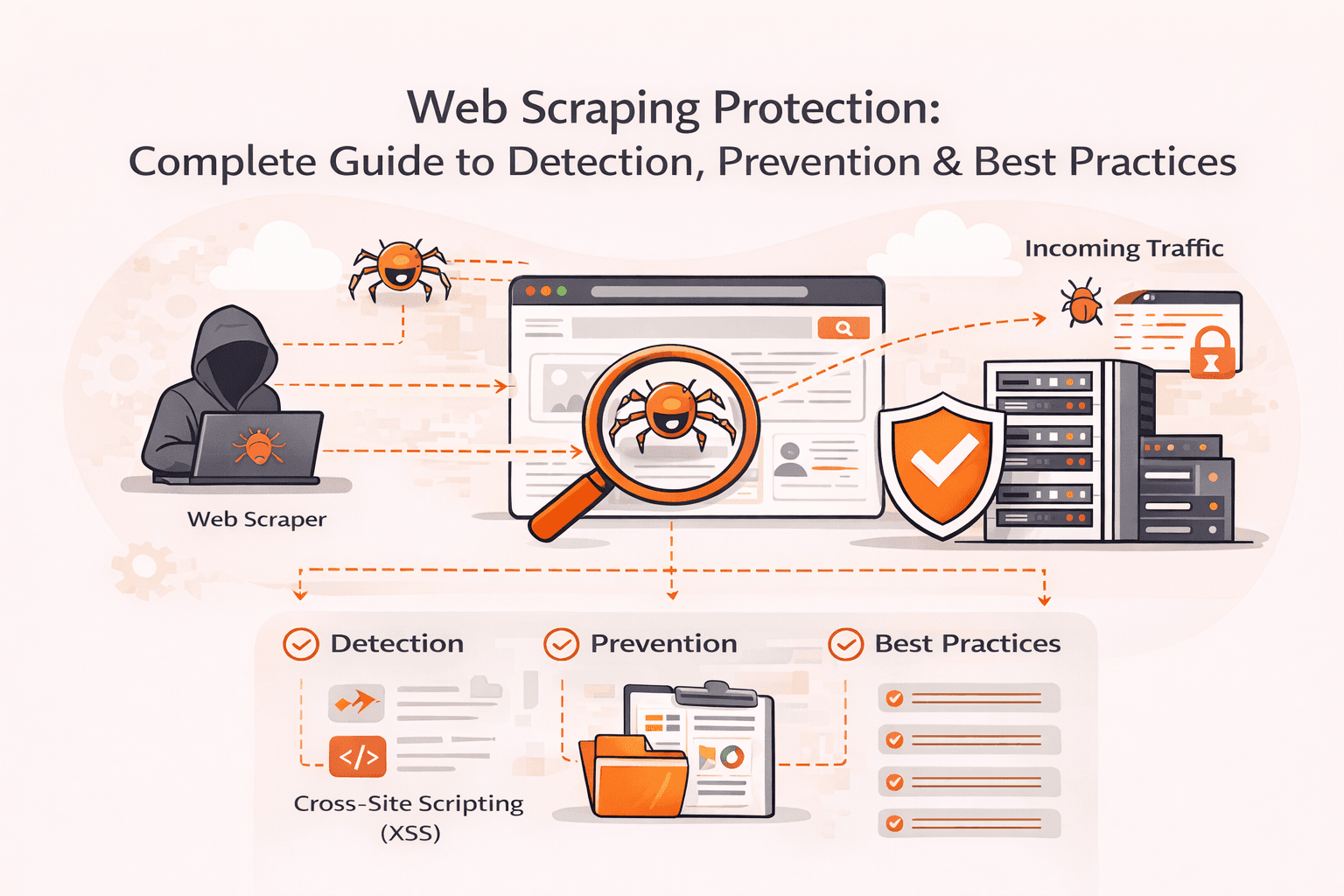
Your server load suddenly spikes by 400%. Legitimate customers can't access your site. Competitors are methodically copying your product descriptions, pricing data, and proprietary content. Modern scraping bots are draining your resources a
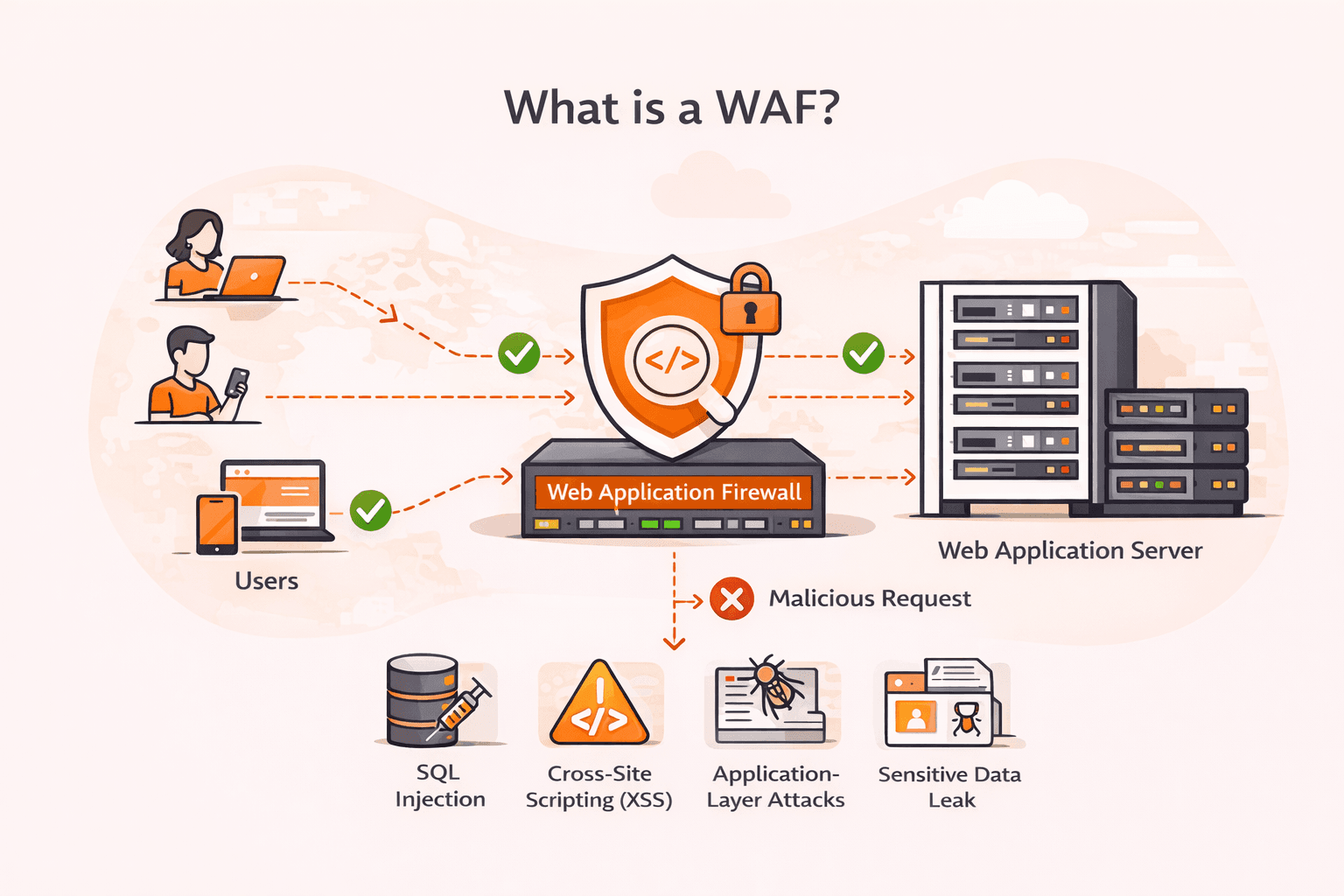
Your web application just processed what looked like a normal login request, but it was actually an SQL injection attack that exposed your entire customer database. Cross-site scripting (XSS), SQL injection, and other application-layer atta
Subscribe to our newsletter
Get the latest industry trends, exclusive insights, and Gcore updates delivered straight to your inbox.